Your own personalised stalker
It always seemed slightly creepy that your computer shows advertising that is strangely accurately targeted at things you might have been interested in. On the surface, that seems quite useful. If you have to tolerate ads on your screen, at least having them show things you were interested in seems helpful.
Instead, we wonder how the system knows. It feels like a breach of our privacy.
It all starts when you install an app, and it pops up a question asking for permission to use your location, and/or your camera and/or your microphone.
This is useful for advertisers. For example, they can use your location. If the app reports this back to the content provider, they can match up your location and compare you to other people nearby. If you tend to go to the same places as other people, you are probably interested in the same things, so an advertiser might use that assumption to present advertising to you, or other people that you spend time with.
That does sound a bit overreaching, but we reluctantly agree to the presented terms simply because we want to use the app. If that is a condition of use, and we want to use the app, then we agree.
So, now we are seeing consumers getting the choice to push back.
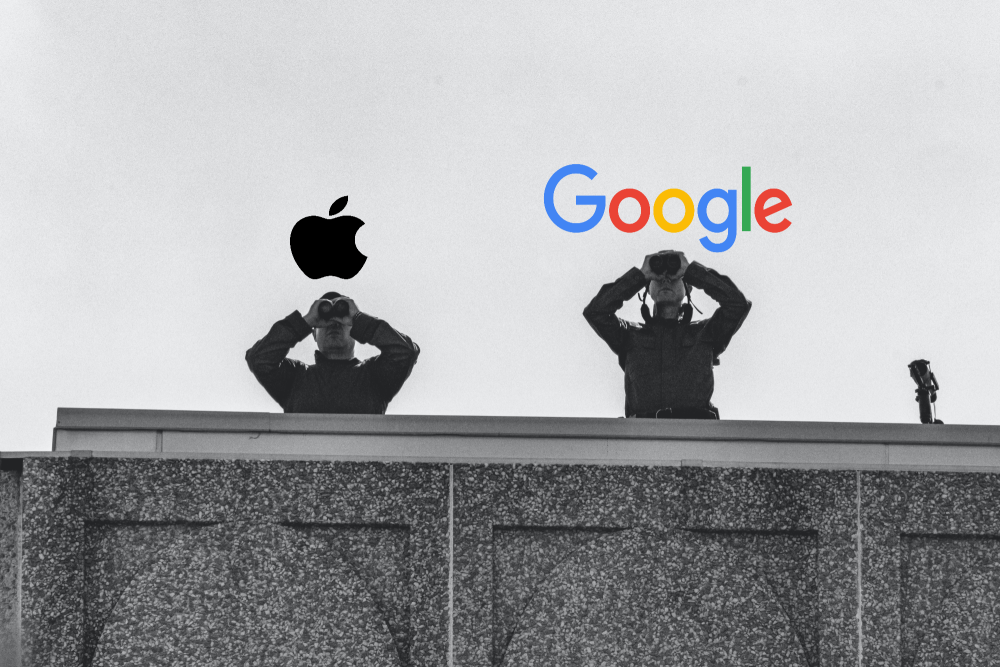
Apple
Now, with iOS15, Apple are saying that you will get to see what apps are accessing your data. You will be able to see when an app used that permission, and there it was sent to. Whether that list of third party sites is any use or not is meaningful is unclear.
Not quite as advanced but following quickly behind is Google Android. With Android 12, you will have the option to de-personalise your data. They will still track usage, but won’t link it back to you.
Is there any truth to the rumour that your phone or TV is listening to you, and presented content based on private conversations it overhears?
Given how poor the voice recognition is on phones , cars, or tools like Alexa or Siri, its pretty evident this can’t be reality. If it, is, then heaven only knows what it thinks it’s hearing. The voice recognition tools are getting better all the time, but there is a long way to go.
Webinar Replay -Enhancing Your Security Posture with Microsoft Secure Score
This webinar replay covers the essentials of Microsoft Secure Score. Secure Score is a powerful tool designed to help businesses assess and improve their security across Microsoft 365 workloads. We will explore what Microsoft Secure Score is, why it is crucial for...
Webinar Replay – 5 mistakes people often make with passwords and how to overcome them
Passwords are the first line of defence against cyber threats. However, many people still make common mistakes that leave their accounts vulnerable. Watch this video for a 30-minute webinar where we will discuss the most frequent password pitfalls and how to avoid...
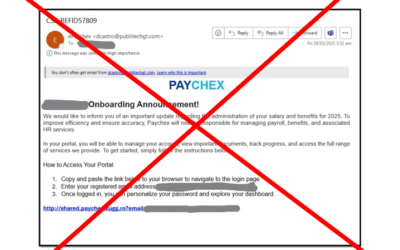
Who’s been paying attention?
We’re really proud of our clients! Last week, these little pieces of ill-intentioned mischief popped up for a couple of the businesses we look after.They were smart enough to evade anti-spam software but not the cyber-training. Although the emails look legitimate,...
Don’t let these common security gaps take your business down.
We’re only a few months into 2025, and already we’ve seen businesses hit hard by cyberattacks they could have prevented. Every time we conduct IT security checkups, we find the same critical vulnerabilities—gaps that could lead to serious downtime, data loss, or...
NCSC warns law firms
It’s not surprising that legal practices are targeted by cyber-criminals.By their very nature, they hold considerable amounts of private “PII” data (personally identifiable information). On top of that, law firms are typically busy, pressured environments where it is...
Webinar Replay – What are the NZ Government recommendations for SME Business cyber-security?
What are the NZ Government recommendations for SME Business cyber-security? How does your business match up?CertNZ has been rolled into the new National Cyber Security Centre. They've released the 10 Critical Controls and a Cyber-Security Framework? What do they mean...
That day when a Kinetics client DIDN’T get hacked.
We’ve just wrapped up a security investigation for one of our amazing clients. All of our clients are amazing, but as you read this story, you’ll see why we’re especially proud of this client. We’ve anonymised it out of respect, although this story reflects really...
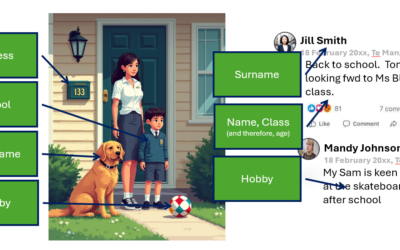
The Hidden Dangers of Oversharing Family Photos on Social Media
In today's online age, sharing family photos on social media has become a common way to stay connected with loved ones and document precious moments. But beware of ‘Oversharing’ There is a huge danger that this seemingly harmless activity can expose you and your...
TEN things the government says you need to know about your cyber-security defence
Regular readers will be a little tired of hearing us talk about cyber-risk and the threat of hackers. You'll forgive us a little because we see the impact when events happen, and we spend our days protecting our clients to keep them safe. But we're just a tiny cog...
What do Microsoft’s Upcoming 2025 Security Enhancements for Windows mean for you?
In response to the significant CrowdStrike meltdown last summer, which exposed some critical vulnerabilities in the Windows platform, Microsoft is set to introduce a series of further security updates in 2025. The meltdown, caused by a flawed update, led to widespread...