What expert cyber-security does my business need?

The inconvenient facts about Cyber Security
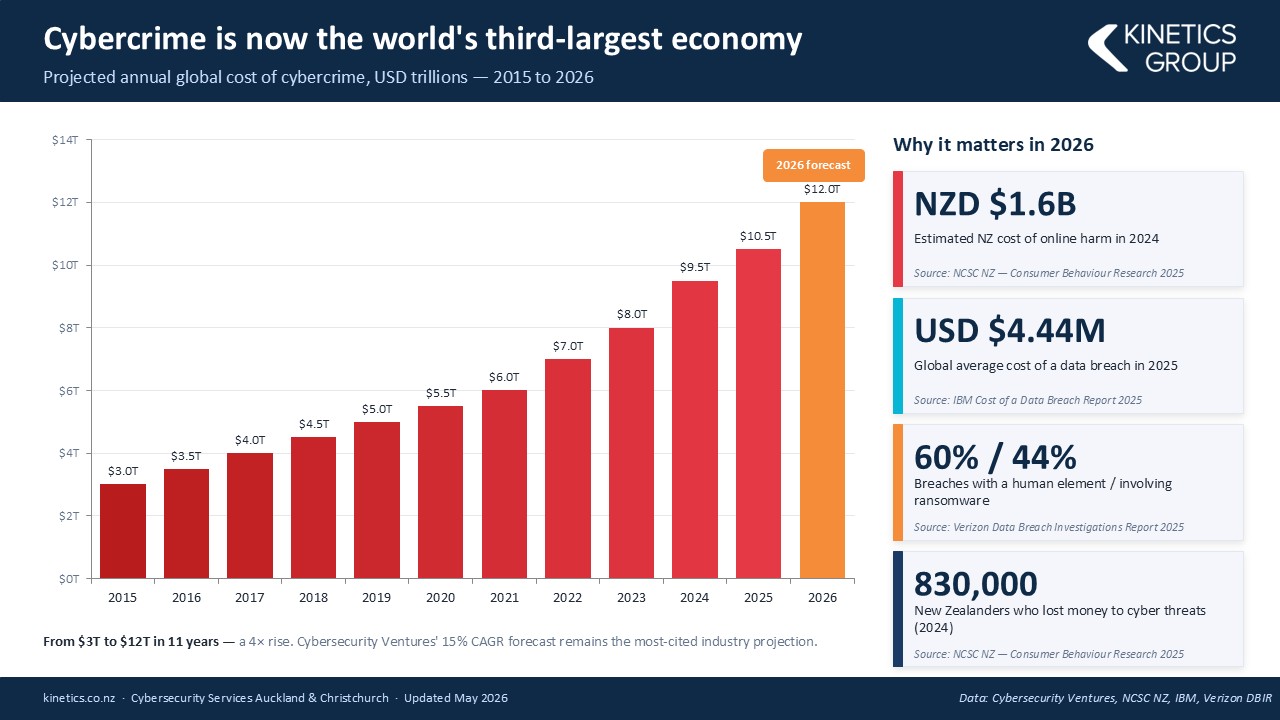
- The number and value of incidents is increasing.
- Cyber Crime is BIG business and they keep investing in new tools.
- If you aren’t keeping your defences up, then it is only a matter of time before you fall victim (i.e. if your cyber protection is the same now as it was even just one year ago, then you are increasingly vulnerable.
- You have to ward them off every hour of every day, they only have to get through once.
You might say this is scare-mongering. If all this hacking is going on and nothing has happened yet, then surely I don’t need to worry?
We’d say “good luck to you – why do you have seat belts in your car? – its only a question of time.”

What Cybersecurity Protection Level Do You Need?
Q: Does this mean I don’t need cyber-insurance? A: You still need cyber-insurance. We can only reduce your risk (and most insurers will want to see these protections in place before they will offer cover)
Q: What is involved installing KARE? A: Once a PC, Mac, Tablet or Phone is ready, our scripts run every time you login and the security tools auto-install – with configuration for corporate devices and BYOD.
AD HOC
STRUCTURED LAYERS based on the CertNZ Critical Controls Framework
For organisations in the cloud with minimal reliance on IT.
Everything is in the cloud. There are only a few PCs/Macs and iPhones/Androids to protect.
For organisations in the cloud, and maybe a small number of servers, looking to be more thorough.
Add in depth reporting, server backup and identity monitoring.
Pick KARE FOUNDATION SME
For organisations that value a structured, proactive and comprehensively protected IT.
Add more scrutiny and awareness, personalised cyber training and business planning.
For organisations in the cloud with minimal reliance on IT
Everything is in the cloud. There are only a few PCs/Macs and iPhones/Androids to protect
For organisations in the cloud, and maybe a small number of servers, looking to be more thorough
Add in depth reporting, server backup and identity monitoring
Pick KARE FOUNDATION SME
For organisations who value a structured, proactive IT engagement
Add more scrutiny and awareness, personalised cyber training and business planning

Enhanced Security Services & Add-Ons
+ Choose additional services as required
Add Fixed Monthly Support Fee
No cost surprises. One fee for all business-hours support
(excludes projects and training)
Add Managed Firewall
Network firewall
Kinetics supplies and manages on a monthly contract
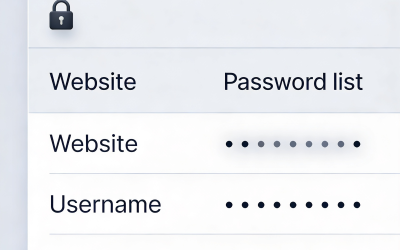
Add Password Vault
Organisation Wide
Maintain unique, complex passwords for all users and/or shared with teams
Add 365 Cloud Backup
Content backup for 365
Go over and beyond the standard Microsoft backup protection
Backup and Continuity
A range from backup to stand-by services
If you have servers, you need to back them up

How about the broader cyber-framework?
Comprehensive Data Protection & Compliance
Platform Security is just part of a broader cyber-security and data protection framework.
Have you considered how manage your data within your Microsoft tenancy? How’s your Microsoft “Secure Score“? As you get the external security set up, let us work with you to manage the other side – your internal security.
Our consultants can work with you to understand what data your organisation maintains, and the obligations (and client expectations) and the rules that need to be established to protect it. Who should have access to which libraries? What can be shared and what can’t be. How do you work with external partners and protect your content?
We can document your data policy, prepare your data privacy policies, incident response plans and data management structures, and we can set up compliance regular reporting.
We’ll implement the policies in your 365 and manage your data to make sure it’s where it should be, not suffering from duplication confusion or unintended leakage
Data Management
The tidier your data, the easier it is for AI to use it well to accelerate your productivity
Download our latest executive “10 minute” briefing to share with colleagues

Latest Cybersecurity Insights & Resources
Microsoft Edge Exposes Saved Passwords
Is you browser giving your passwords away? If your team uses Microsoft Edge and saves passwords in the browser, every one of those credentials is sitting in plain, readable text in your computer's memory from the moment Edge launches. A security researcher has...
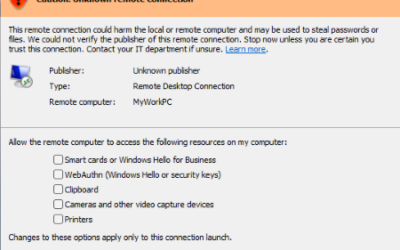
That New Windows Warning About Remote Desktop? Don’t Ignore It.
If you've opened a Remote Desktop connection file today and been greeted by an unfamiliar orange warning banner: "Caution: Unknown remote connection" then you are not imagining things. Microsoft has introduced new protections as part of its April 2026 cumulative...
Webinar Replay: Beyond Antivirus: Understanding MDR and ITDR for Modern Cyber Defence
Your traditional security isn't stopping today's attacks. Here's what will. The Problem Every NZ Business Faces Your business has antivirus software. You have firewalls. You've implemented email filtering. Yet cybercriminals are increasingly successful at bypassing...
When “Legitimate” Tools Are Used Illegitimately (like booking a meeting time)
Cyber awareness isn’t just about blocking malware — it’s about recognising intent. Recently, we received a callout from a client after a user received what initially appeared to be a genuine business opportunity. The email exchange seemed credible, replies were...
Could you get into trouble with the law if you lose a USB stick?
A lost USB stick can be a notifiable privacy breach. Here’s why that matters It sounds old school, but USB sticks are still floating around plenty of NZ businesses. A recent draft decision note from the Office of the Privacy Commissioner is a timely reminder...
Additional M365 Security Protection Rolled Out for our KARE Foundation Customers
Turning up your cyber-security Kinetics is busy rolling out an additional security protection for Kinetics KARE Foundation customers only, designed to stop a highly active and sophisticated phishing campaign currently targeting Microsoft 365 environments worldwide. ...
Your (Home/Small Business) Router Could Be Working for Criminals Right Now
Right now, somewhere in the world, a home or office router is quietly routing cybercriminal traffic, and its owner is completely unaware. That's the reality revealed by the discovery of KadNap, a sophisticated malware campaign that has become one of the most...
When Geopolitical Conflict Becomes Your IT Problem
Lessons from the Stryker Cyberattack A global medical technology company. 56,000 employees. Operations in 60 countries. And in March 2026, systems wiped across every one of them — not because of a data breach or ransomware, but because of a school bombing in Iran....
When AI Becomes the Attack Tool
What the Mexico Government Breach Means for Your Business A cyberattack that unfolded over December 2025 and January 2026 has changed how security professionals think about AI . New Zealand business leaders should take note. A single attacker jailbroke Anthropic's...
Your Phone Is a Target
Why Mobile Security Can't Be an Afterthought Think about everything on your smartphone or tablet right now: your email, your banking app, Microsoft 365, client communications, multifactor authentication codes, and a direct line into your company's cloud systems. Now...