Your own personalised stalker
It always seemed slightly creepy that your computer shows advertising that is strangely accurately targeted at things you might have been interested in. On the surface, that seems quite useful. If you have to tolerate ads on your screen, at least having them show things you were interested in seems helpful.
Instead, we wonder how the system knows. It feels like a breach of our privacy.
It all starts when you install an app, and it pops up a question asking for permission to use your location, and/or your camera and/or your microphone.
This is useful for advertisers. For example, they can use your location. If the app reports this back to the content provider, they can match up your location and compare you to other people nearby. If you tend to go to the same places as other people, you are probably interested in the same things, so an advertiser might use that assumption to present advertising to you, or other people that you spend time with.
That does sound a bit overreaching, but we reluctantly agree to the presented terms simply because we want to use the app. If that is a condition of use, and we want to use the app, then we agree.
So, now we are seeing consumers getting the choice to push back.
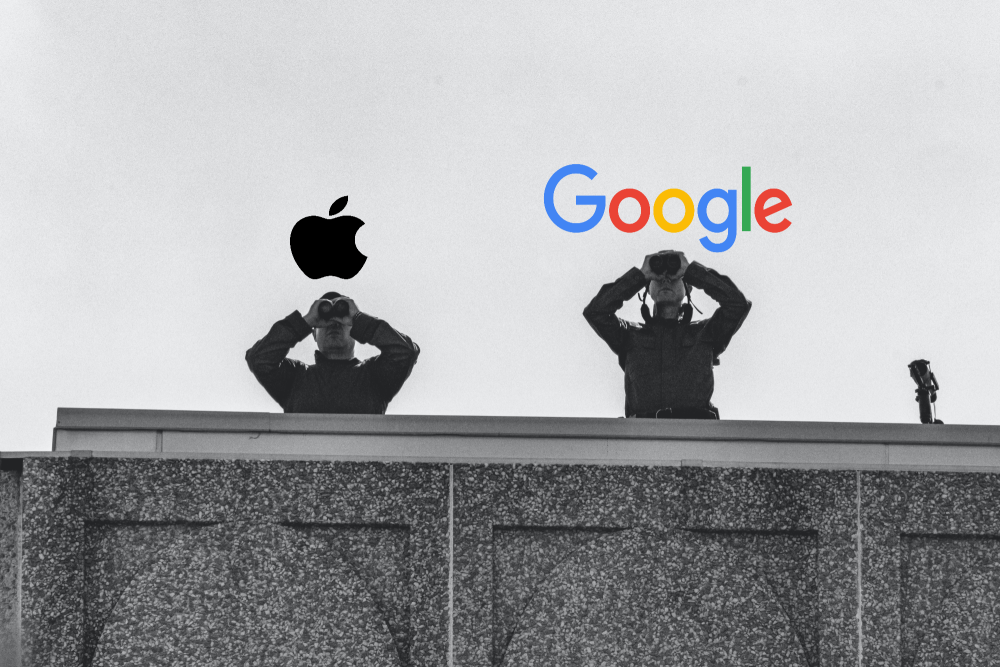
Apple
Now, with iOS15, Apple are saying that you will get to see what apps are accessing your data. You will be able to see when an app used that permission, and there it was sent to. Whether that list of third party sites is any use or not is meaningful is unclear.
Not quite as advanced but following quickly behind is Google Android. With Android 12, you will have the option to de-personalise your data. They will still track usage, but won’t link it back to you.
Is there any truth to the rumour that your phone or TV is listening to you, and presented content based on private conversations it overhears?
Given how poor the voice recognition is on phones , cars, or tools like Alexa or Siri, its pretty evident this can’t be reality. If it, is, then heaven only knows what it thinks it’s hearing. The voice recognition tools are getting better all the time, but there is a long way to go.
Is Ignorance Bliss?
Are there things you would rather not know? If those things were about you, and could impact you, would that change your answer?Sometimes a regular check-up can reveal information that you would rather not know – whether it’s getting your car serviced, and finding out...
Should we worry about DeepFake?
What can you believe? For years we've told you that you can't believe every email you read. But now we can't believe every photo or video you see. Deepfake is the term for when a picture, video or audio file is altered to put a different person into the content,...
Webinar: Updating what is ‘reasonable’ to protect your organisation from cyber-crime.
Cyber-security gets harder, so we make it easier. Much as the heading may sound 'double-dutch', it isn't. Simply, the levels of protection that are 'reasonable' to protect your organisation have changed. We need to do more, and at Kinetics we know that...
What’s a passkey? What do they mean for my password?
Every time you sign up for something new, it seems you have to think up a new password. Sometimes you can use your Google or Facebook credentials but more often than not, you have to use your email address and come up with a new password. The lazy amongst us reuse...
Cyber-attacks on emails get faster and faster
A lot can happen between your morning coffee and your lunch. That’s all it takes to go from ‘normal’ to ‘disaster’ when the hackers strike. Microsoft researchers recently worked backwards through a ‘BEC’ attack (business email compromise – IT people love to convert...
When KARE isn’t enough
The world has changed... Since we designed our original ‘base’ KARE plans, the world has gone more mobile, more in the cloud and ‘work-from-anywhere’ is ubiquitous. And the cyber-threat environment has become much more adverse. Our KARE plans need to reflect 2023! In...
How cybersafe are you at home?
The NSA have released a ‘Cybersecurity Information Sheet’ for home networks. We know that home networks can range from simple to complex. You might have smart TVs, smart home lighting, Google Home, Alexa, alarms, cameras – the list goes on. These devices can be less...
Warning : Business Email Compromises skyrocket
The stats are in, and they are alarming! Business Email Compromise (BEC) attacks are up 81% in 2022! Small Medium Businesses often say to us that they don’t need to worry about cyber because they're not worth it for an attacker. Unfortunately, that’s incorrect. There...
Is automated Microsoft patching enough?
Microsoft have been releasing patches for 30 years. It’s easy to become blasé about them. Yes, Microsoft can automatically apply updates to Windows and Office. But that does not mean that you can rely on it. Any system is only as good as how well it is monitored....
Beware of “Pig-Butchering” – a new trend in Social Engineering
Where do these names come from? The latest trend is referred to as Pig-Butchering. The name comes from the Chinese underworld (shāzhūpán). The term refers to fattening up a pig, taking a longer-term view. They develop their target slowly, looking to get maximum...









