What expert cyber-security does my business need?

The inconvenient facts about Cyber Security
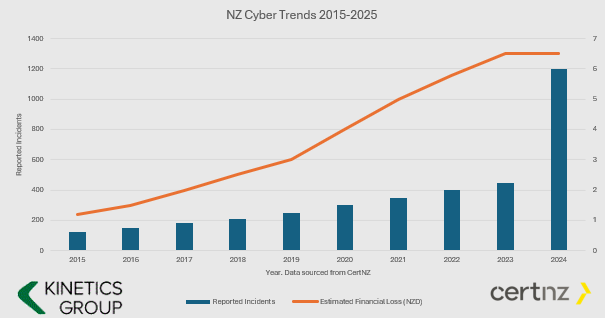
- The number and value of incidents is increasing.
- Cyber Crime is BIG business and they keep investing in new tools.
- If you aren’t keeping your defences up, then it is only a matter of time before you fall victim (i.e. if your cyber protection is the same now as it was even just one year ago, then you are increasingly vulnerable.
- You have to ward them off every hour of every day, they only have to get through once.
You might say this is scare-mongering. If all this hacking is going on and nothing has happened yet, then surely I don’t need to worry?
We’d say “good luck to you – why do you have seat belts in your car? – its only a question of time.”

What Cybersecurity Protection Level Do You Need?
Q: Does this mean I don’t need cyber-insurance? A: You still need cyber-insurance. We can only reduce your risk (and most insurers will want to see these protections in place before they will offer cover)
Q: What is involved installing KARE? A: Once a PC, Mac, Tablet or Phone is ready, our scripts run every time you login and the security tools auto-install – with configuration for corporate devices and BYOD.
AD HOC
STRUCTURED LAYERS based on the CertNZ Critical Controls Framework
For organisations in the cloud with minimal reliance on IT.
Everything is in the cloud. There are only a few PCs/Macs and iPhones/Androids to protect.
For organisations in the cloud, and maybe a small number of servers, looking to be more thorough.
Add in depth reporting, server backup and identity monitoring.
Pick KARE FOUNDATION SME
For organisations that value a structured, proactive and comprehensively protected IT.
Add more scrutiny and awareness, personalised cyber training and business planning.
For organisations in the cloud with minimal reliance on IT
Everything is in the cloud. There are only a few PCs/Macs and iPhones/Androids to protect
For organisations in the cloud, and maybe a small number of servers, looking to be more thorough
Add in depth reporting, server backup and identity monitoring
Pick KARE FOUNDATION SME
For organisations who value a structured, proactive IT engagement
Add more scrutiny and awareness, personalised cyber training and business planning

Enhanced Security Services & Add-Ons
+ Choose additional services as required
Add Fixed Monthly Support Fee
No cost surprises. One fee for all business-hours support
(excludes projects and training)
Add Managed Firewall
Network firewall
Kinetics supplies and manages on a monthly contract
Add Password Vault
Organisation Wide
Maintain unique, complex passwords for all users and/or shared with teams
Add 365 Cloud Backup
Content backup for 365
Go over and beyond the standard Microsoft backup protection
Backup and Continuity
A range from backup to stand-by services
If you have servers, you need to back them up

How about the broader cyber-framework?
Comprehensive Data Protection & Compliance
Platform Security is just part of a broader cyber-security and data protection framework.
Have you considered how manage your data within your Microsoft tenancy? How’s your Microsoft “Secure Score“? As you get the external security set up, let us work with you to manage the other side – your internal security.
Our consultants can work with you to understand what data your organisation maintains, and the obligations (and client expectations) and the rules that need to be established to protect it. Who should have access to which libraries? What can be shared and what can’t be. How do you work with external partners and protect your content?
We can document your data policy, prepare your data privacy policies, incident response plans and data management structures, and we can set up compliance regular reporting.
We’ll implement the policies in your 365 and manage your data to make sure it’s where it should be, not suffering from duplication confusion or unintended leakage
Data Management
The tidier your data, the easier it is for AI to use it well to accelerate your productivity
Download our latest executive “10 minute” briefing to share with colleagues

Latest Cybersecurity Insights & Resources
Your Customers Need to Trust Your Emails: Here’s How DMARC 2.0 Helps
Yet another IT acronym: "DMARC" DMARC stands for Domain-based Message Authentication, Reporting, and Conformance. It's an email authentication protocol that helps protect your domain from being used in email spoofing, phishing attacks, and other cyber...
Christmas is coming. But will you get a visit from Santa or from a grinchy hacker?
Protecting Yourself from Cyber Threats While on Holiday We're more vulnerable than normal to hackers at this time of year. Unfortunately, the hackers know it and tend to be more aggressive.In the rush up to Christmas, there's normally so much to do that we're all that...
Understanding Your Microsoft Secure Score: Why Your Percentage May Drop (While Your Security Improves)
Important Update for KARE Foundation Subscribers If you've noticed your Microsoft Secure Score percentage decreasing recently, don't be alarmed. Your security hasn't weakened. In fact, Microsoft is making significant enhancements that will ultimately make your...
2025 Q4: Cyber Landscape Update (are you still feeling lucky? New Zealand’s Cyber-threat landscape demands action)
Why This Brief Matters A cybercriminal only has to be lucky once. You have to be lucky every minute of every day. That remains the stark reality for kiwi businesses in Q4 2025. This isn't another dry technical report filled with acronyms and alerts. Kinetics has...
SpamGPT: When AI Becomes a Phishing Playbook—And How to Protect Your Business
For years, we've told businesses to watch for telltale phishing signs: poor grammar, suspicious sender addresses, generic greetings. But what happens when cybercriminals have access to the same sophisticated AI tools your marketing team uses—except weaponised...
The Rise of AI-Powered Ransomware
Unveiling a dark future: The First AI-Powered Ransomware In a groundbreaking discovery, researchers at ESET have uncovered what they believe to be the first known AI-powered ransomware strain, aptly named PromptLock. This sophisticated malware is not just a step...
Webinar Replay: Rethinking Endpoint Security: Smarter Strategies for a Safer Business
Cyber-protection keeps getting more complex, more restrictive and more expensive. This month we are talking with expert Thomas Shobbrook. He updates us on the latest security trends and help us understand how well protected your device is out-of-the-box. We ask...
Webinar Replay – Securing the Mobile Frontier: Cybersecurity Essentials for Phones and Tablets for Modern Businesses
As mobile devices become the backbone of modern business operations, they also present a growing target for cyber threats. Apple or Android - they're both important. Every time you use these to access your Teams, Email or anything else, you are relying on them to be...
Device Code Phishing: A Dangerous New Scam You Need to Know About
Device code phishing is a sneaky new way hackers are stealing people's online accounts. In device code phishing, threat actors exploit the device code authentication flow to capture authentication tokens, which they then use to access target accounts, and further gain...
June 2025 Report: Cyber is now the THIRD largest economy in the world
As we approach the midpoint of 2025, New Zealand’s cyber security landscape continues to evolve rapidly. With digital transformation accelerating across sectors, the country faces a growing array of cyber threats—ranging from financially motivated scams to...