The Trillion dollar industry
At the time of writing, the Waikato DHB cyber-attack is ongoing. The government is refusing to pay the ransom as a point of principle, and it looks like every possible tool at their disposal is being used to try to recover the situation.
Should they just pay the ransom? Or should the government go further and make it illegal to pay ransoms in New Zealand? That’s the question that Minister Kris Faafoi is having to assess at the moment. DHB attack: Why Justice Minister Kris Faafoi won’t make it illegal to pay a cyber-ransom – NZ Herald
Cyber crime is big business. We’ve called it organised crime in previous articles and we’re happy to stick with that. These organisations recruit the best and brightest out of the top universities, and give them both the latest tools and time to wreak havoc. Their recruits are paid astronomical sums to work for them, overcoming any moral objections with immorally large pay checks. These paychecks are funded by the proceeds of previous hacks. Every time they are paid, their war chest is strengthened. For example, we recently saw the Colonial Pipeline in the eastern US get hacked for 75 bitcoins (just under US$4M) which went to a criminal group called ‘Darkside”.


So, will cutting off payments stop their attacks by removing the incentive?
These criminals are smart and highly motivated. They seem to have no conscience but plenty of greed. Waikato is not only the hospital being brought down – there was a huge wave of hospital attacks in the US in October, just a few months ago – Several hospitals targeted in new wave of ransomware attacks – CNNPolitics.
I don’t know how Waikato DHB got infected, but the rumour is that it was from phishing attacks onto machines that weren’t fully patched up to date. We don’t know if that is true, but it is a common attack vector. Once a hacker gets into a system, they often hold back and try to dig further looking for more vulnerabilities they can exploit. The more damage they can cause, the more ransom they can demand, so they will often use one vulnerability to find the next, and so on until they finally have enough to bring the house down.
Security is all about layers. There is NO way to prevent attacks, and it is impossible to guarantee that any system is invulnerable. We saw that with the recent Hafnium attack where a vulnerability was exploited before patches were available to block it. But the more layers of security, the harder you make it, and you reduce the scope of any harm.
Today, even if you have the best backups and can recover the system, the hackers then threaten to release the data you hold to media or competitors. In the case of the Waikato DHB, it is being reported that personal data is being released to media by the hackers to increase pressure, even as they fail to stand their systems up.
As to paying the ransom, I suspect your perspective changes when your business, your job or livelihood is threatened. Not an easy decision and hopefully one we can avoid by being paranoid.
The best solution we can recommend is to check your cyber insurance and to apply the best security you can reasonably afford, which should be more than you had last year. Expect it to be more again next year as new tools and new threats emerge. Consider managed security solutions like our KARE Plans.
We don’t know where this will end, or if it will end, but let’s hope so. It is such a drain on our resources and holds us back from investing in tools that make us more productive.
Are your legacy IT systems giving hackers a backdoor into your business?
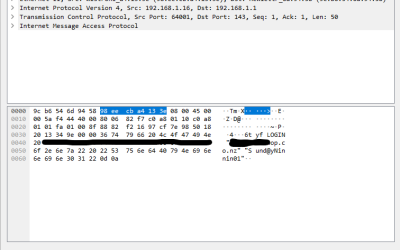
One of our engineers was working on migrating a customer from a legacy email server into Office 365 after we discovered they were under a brute force external attack. The migration required that we receive the users passwords. These would, of course, be reset after...
Service Alert
We're experiencing an extra heavy call volume today and it's proving challenging to respond as quickly as normal. It's been brought on by an apparent Microsoft change resulting in unexpected Windows 11 upgrades. These are happening to a number of devices even if...
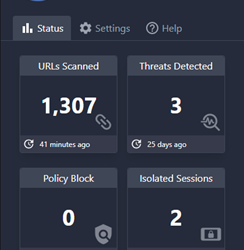
Breaking news: New protections added to Kinetics KARE Foundation
We have big news for Kinetics customers on our “KARE Foundation” cyber plan. We've added new Browser Cyber-Protection We’ve found an amazing new security tool called ‘Conceal' that provides even more added protection. Cyber-security is all about layers and this one...
Penetration Testing
Penetration testing is important for businesses because it helps them identify and fix security vulnerabilities before they can be exploited by attackers. It can be a significant job as it needs a team of security professionals to simulate a real-world cyberattack....
What would you do?
Imagine – you are busily going about your day when suddenly your meeting is interrupted. “No one can access their files!!!” or “We just accidently paid $50,000 to a fraudulent account and we can’t get it reversed!!!” or something similar. What would you do? Where...
Security Updates
We need to make some security changes. These are in accordance with the continued work by Microsoft to protect 365 users. This will keep your configuration current with their latest advisories but may have some (limited) impact on your IT experience. It is all about...
Layered Security Works
There is no silver bullet in cyber-security. Best practice requires layers of protection. One of those layers is ‘geo-blocking’, which means you can only log in from specified countries and overcomes many of the African and Eastern European hacker fraternities....
Look out for LinkedIn Smart Links
This is a great example of needing new tools that didn't used to exist, to keep cyber-safe, even if they add cost to our cyber-protection. Hijacking your trust in LinkedIn Cybersecurity firm Cofense have detected phishing campaigns that used LinkedIn links called...
Would your cyber-security have saved you from this hack attempt?
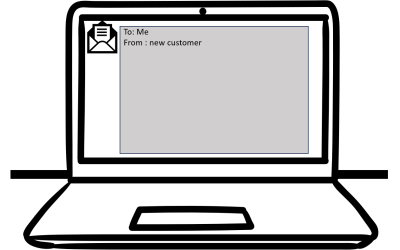
This is a real and very clever 'spear-phishing' attempt that one of our legal clients in Auckland received today.Would you have opened it? Would your IT have protected you?To: Me From : new customer Hello, My Husband and I are looking to buy a property (First-time...
Is it really you?
News that an elderly woman was tricked out of $100,000 over Facebook won't be a surprise to regular readers. She was fooled into thinking she was talking to a friend, and then sending money to access some make-believe Covid fund. AI makes it easy to speak in...